Think about how happy you are when you first get your new phone. If you are like most of us you can’t keep your hands off of it. You try all the new features out and mutter to yourself, “wow, this is so cool”. The enthusiasm that people have for their new mobile devices can be a major benefit for the company they work for, too. Today, we are going to discuss how, with all the features and powerful computing power, you can work effectively on your smartphone.
Washington Works Blog
As much as we hate to admit it, the first thing that many people still think of when they hear the term “tech support” is the experience that comes with an antiquated approach to technology services: the break/fix method. Fortunately for us, we are seeing many businesses make the better decision, and turn to the clearly superior option, managed IT.
COVID-19, or coronavirus, has been a major global health concern over the past couple of months. At this point, it is clear that this disease could have serious impacts on the workplace. We wanted to provide a brief rundown of good workplace and network health practices, as well as a few pointers on how you can handle health-based employee absences.
The modern business has to deal with a lot of potential security problems. Today’s threat landscape is filled with people looking to prosper off of your misfortune. As a result, doing what you can to maintain the security of your network and data is essential. Today, we will discuss how maintaining your organizational cybersecurity doesn’t have to be costly or time consuming.The best way we’ve found to go about doing this is by highlighting a few key actions that you can take to keep your network secure and your data safe.
Windows 7 might not be supported by Microsoft any longer, but millions of people are still using PCs that run the antiquated operating system. Since Microsoft has put an end to extended support for Windows 7 OS, a couple bugs have been found. Let’s take a look at what exactly is behind these issues and discuss your options.
The small businesses that rely on technology typically logs a lot of phone time with technology vendors. Decision makers that may not know more than the average person about IT can be left making important technology decisions when they think they are just making financial decisions. Today, we’re going to explain how they are different and what your next step is.
It wasn’t too long ago when the idea of video conferencing was a very complicated one. The technology just wasn’t there to make it a major benefit for companies. As conferencing technology has been innovated upon, however, it now presents a laundry list of substantial benefits. Let’s take a look at some benefits you can see by moving to video-driven meetings.
With most businesses looking to control costs, their decision makers need to find innovative new ways to do business. One way that many firms can increase productivity without raising costs is to promote a culture of collaboration. Today, we’ll take a look at some of the useful technology that businesses can leverage to improve their output.
Organizational cybersecurity has to be a priority for every business. These days, companies are getting hacked left and right and being exposed to some of the very worst malware ever created. Today, we will take a look at some cybercrime statistics that will put in perspective just how damaging cybercrime is.
Augmented reality has been one of the most cited emerging technologies for the past few years. It was the technology that was supposed to fuel Google Glass, the failed attempt at creating a pair of revolutionary smart glasses. Since then, there hasn’t been much press about AR in the mainstream media and not much is known about major tech companies’ attempts to improve AR technology.
Most companies have some sort of regulation they need to stay compliant to, and 2020 seems to be a landmark year. This year, companies have to deal with end-of-life upgrades, the development of new privacy laws, as well as the existing regulatory landscape. Let’s take a look at why compliance is important and what to expect in the year ahead.
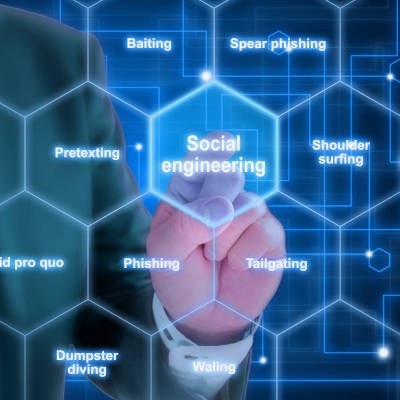
As prevalent as cybersecurity threats unfortunately are today, many users tend to overlook major threats that they just aren’t focused on nearly as much: social engineering attacks. Social engineering attacks are just another means for a cybercriminal to reach their desired ends, and therefore needed to be protected against.
How often do you find a message in your SMS inbox that has clearly come from a business, but you almost have to wonder, simply because the incoming number seems to be randomized? Google has taken notice of this challenge, and so has rolled out a means for businesses to confirm that they are in fact the ones sending a particular message.
Microsoft has a well-developed reputation for creating software that enables users to achieve their work objectives, especially in the business setting. Here, we’re diving into a few capabilities of one such software title, OneDrive, to review some of the features that a user might want to take advantage of.
The curious thing about information technology is that, while it improves as any other technology would, the environment can accelerate the various changes made to it at various rates. As a result, knowing when your business needs to upgrade its technology isn’t always so cut-and-dry. To help, we’re sharing a few clear indicators that hint that the time has come.
IT administrators are pretty particular about what software is used on the networks that they manage. This is not because we have any vested interest in the software itself, it’s because of the inherent reliability of the software they manage. They’ve tested it, they manage it, they know it. When an organization starts dealing with employee-downloaded software--especially if there is no procedure in place to report additions to IT--they can quickly lose control over the network.